create virus using c langauge | .::APAJR::.
This program is an example of how to create a virus in C. This program demonstrat…
?-: Shutdown Command Via Command Prompt :- | .::APAJR::.
?-: Shutdown Command Via Command Prompt :- The 'Shutdown' Command Becom…
Footprinting And The Basics Of Hacking | .::APAJR::.
-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-…
[Tutorial] How To Setup Cybergate RAT by Port Forwarding | .::APAJR::.
Hello! You might know me from the stickied Cybergate tutorial in the CG section.. BUT…
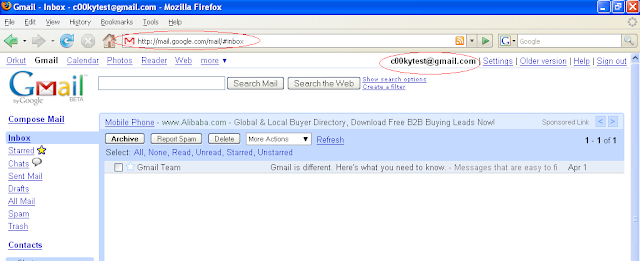
Gmail Session Hijacking in 7steps | .::APAJR::.
Session tokens are crown jewels of user identity on a web application. It's no hi…
hack website using backtrack sqlmap | .::APAJR::.
Today i will teach you all, how to hack website admin password using back track. …
Notepad Tricks: Cool Notepad Virus tricks for Windows | .::APAJR::.
Notepad, the text editor that comes bundled in Windows is an excellent tool for text …
How to learn SEO | .::APAJR::.
If you’d like to learn SEO the Distilled way, enrol in our online SEO University – Di…
Learning SEO Online, the Best Places to Get Started | .::APAJR::.
I always have to chuckle when people ask me what university or school I went to learn…
Get Started with the Beginner's Guide to SEO | .::APAJR::.
New to SEO? Need to polish up your knowledge? The Beginner's Guide to SEO has…
Nobody can create a FOLDER anywhere on the computer which can be namedas “CON”. | .::APAJR::.
[caption id="attachment_21" align="alignnone" width="470&quo…
Text message Hide in Image | .::APAJR::.
Hi Guys. Today we will see how to hide Text Message in any image file. This is a…
Session Hijacking Facebook Accounts | .::APAJR::.
This is a tutorial that demonstrates just how simple it is to get access to facebook …
Top 10 Ways to Hack Facebook Accounts | .::APAJR::.
Facebook is one of the most widely used social networking site with more than 750…






Social Plugin